
How Kimsuky Hackers Exploit Loose DMARC Policies to Master Email Spoofing

North Korean cyber operatives from the group known as Kimsuky are refining their methods to sidestep anti-spam filters and employ tracking pixels in their email campaigns, cybersecurity researchers report.
The group, notorious for its cunning use of social engineering to target a variety of entities including think tanks, government organizations, and journalists, aims to gather sensitive intelligence about international perspectives on North Korea.
Email communication is a cornerstone of Kimsuky’s strategy. The group leverages email for dual purposes: to distribute malware through attachments disguised as legitimate documents and to directly solicit intelligence by posing as journalists or think tank representatives. According to a recent analysis by cybersecurity firm Proofpoint, the group, also referred to as TA427, APT43, and Velvet Chollima, often prefers direct engagement over relying solely on infected software to gather information.
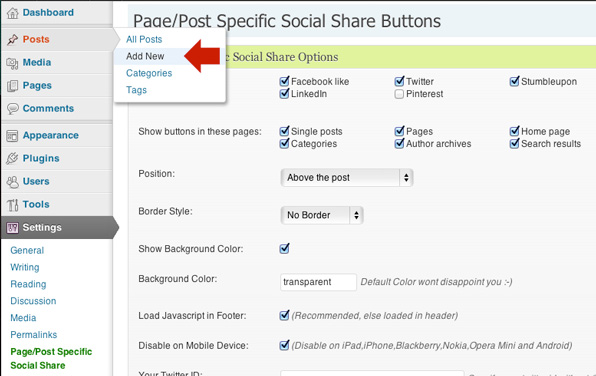
One of Kimsuky’s tactics includes exploiting vulnerabilities in DMARC (Domain-based Message Authentication, Reporting and Conformance) policies. DMARC helps prevent email spoofing by enabling recipients to verify if emails genuinely originate from the stated domain, using a combination of digital signatures and designated IP address verifications. However, Kimsuky targets organizations with DMARC policies set to “none,” which ignores failed authentication attempts, allowing the group to send emails that appear to be from credible sources without hindrance.
Furthermore, the group has begun incorporating tracking pixels into their emails. These small, hidden images provide Kimsuky with data about whether an email was opened, when it was opened, and the type of device used, serving as a tool for initial reconnaissance to confirm active email addresses and gather basic information about the recipient’s network environment.
High-profile institutions such as the Stimson Center, the Atlantic Council, and the Wilson Center have been impersonated by Kimsuky in these phishing operations. Despite being subjected to financial sanctions by the Biden administration in the previous year—a largely symbolic gesture, given North Korea’s isolation from the global financial system—the group remains active. The U.S. Cybersecurity and Infrastructure Security Agency notes that Kimsuky has been operational since 2012 and has used more than 100 different domains in its campaigns.
Greg Lesnewich, a senior threat researcher at Proofpoint, remarks on the group’s expertise in social engineering and its creative exploitation of DMARC to bolster the authenticity of its phishing efforts, highlighting the group’s sophisticated approach to cyber espionage.






























Recent Comments